Yahoo Mail security Update your access
Yahoo Mail is one of the companies with most road in the email world and related services; unfortunately, it cannot say it is the first in its class, but being indeed one of the most competitive and stand out in the history of the internet. Recently, Yahoo! went through a strong situation of informatics vulnerability, which exposes personal data of thousands of users.
Therefore, Yahoo mail has responded with a complete reinvention of itself, but it is calling on the users to be cautious in relation their personal data, recommending to update the authentication information in order to avoid any chance of unauthorized access to the account, since regardless of the improvements on security matters, there nothing to be done on the already stolen data.
Yahoo Mail Change your password as soon as you can
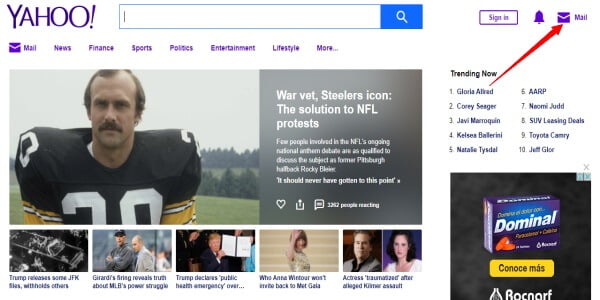
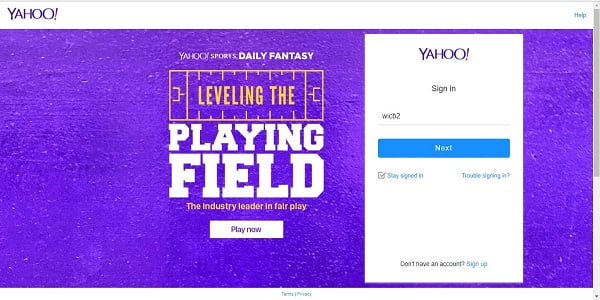
Changing the password is going to guarantee that your personal data will be safe, and on the new Yahoo! interface doing this is a very simple task. In order to do it, access your Yahoo! account trough the log in registration, which you can access by clicking the persistent Log In button on Yahoo! ´s home page.
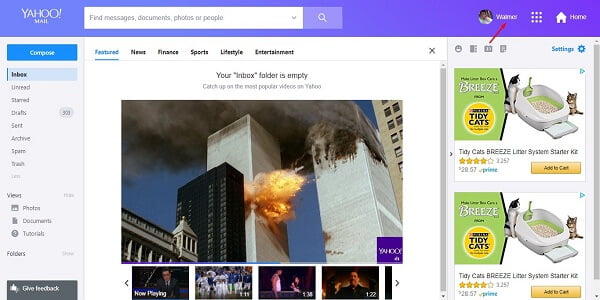
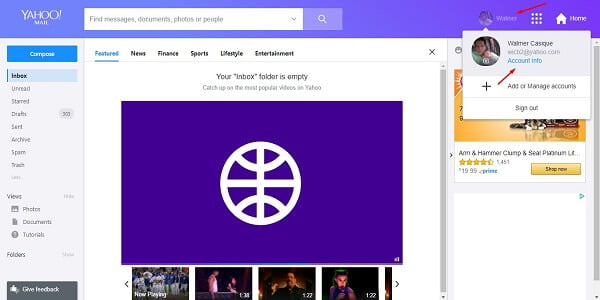
After you are on your mail box, click on the profile button that is where you can also log out.
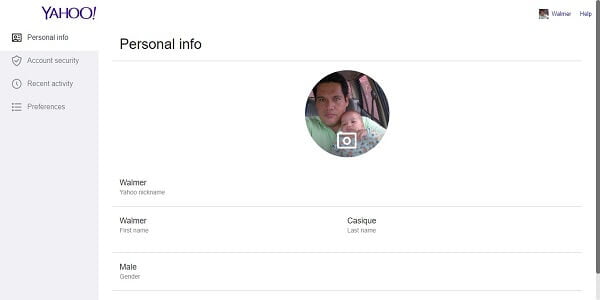
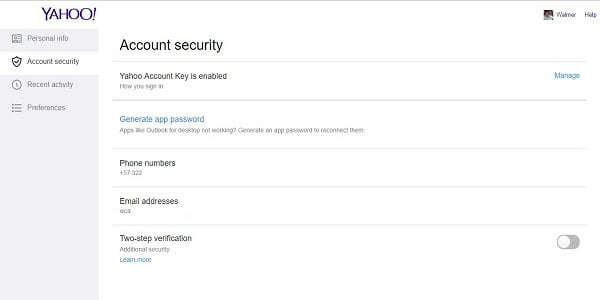
By clicking on it, a new tab will be opened where all the account information is loaded. After this, you must click on Account Security to be able to change the password.
For safety, it will be requested for you to log in again so the options related to password changing could be shown. After that, click on Change Password to perform the corresponding procedure.
As an advice, it is recommendable that the new password to be the same or superior to the 8 characters that consists on capital letters, minor letters, numbers and special characters.
Not only can the email password be changed
The option on changing the password to guarantee the security on the access account is not the only option that is available directly on that particular portal, but other options like changing phone number and email address are available as well.
In details, there is a powerful reason for you to change and update this information that is part of your personal data; if you were one of the users that was hacked during the computer attacks on Yahoo´s platform, it means that the related data is on the possession of the attackers.
When you update your personal data, the association of your personal information gets loose of these contact data, so the information updating is justified. To change it, there just have to be a clicked on the value to start the corresponding data update process.
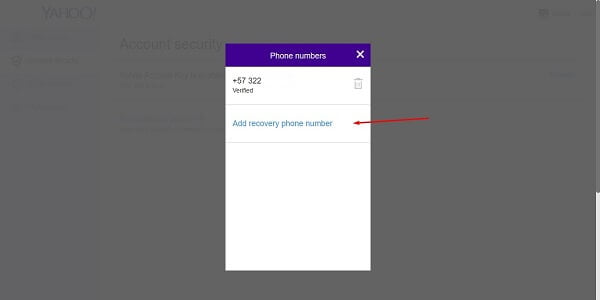
Specifically, the update process consists on adding new phone numbers and email addresses and remove the current one, you just have to pick the corresponding options to achieve these goals. For example, the option on generate a password app is used if after the computer attack you had linked your accounts from other providers to Yahoo! and then you changed your accessing data.
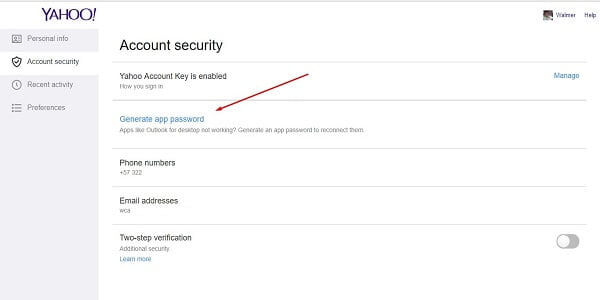
In the same way, updating this data will allow providers of other email and service accounts to work again with your new Yahoo Mail account.
Other useful options of contact and security information
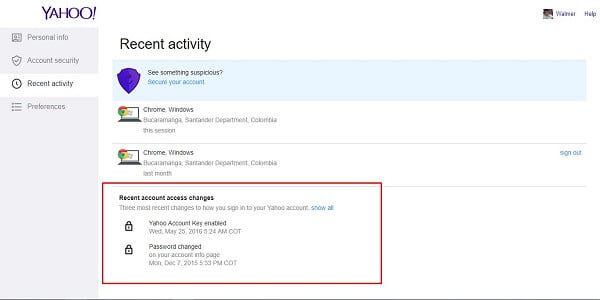
On another topic, when accessing the Account Information option personal data can be shown and security information can be updated as well like in the previous title. However, it can also be shown the recent activity that is a registration process to the account, which gives information about place, date and devices where log in process is performed from.
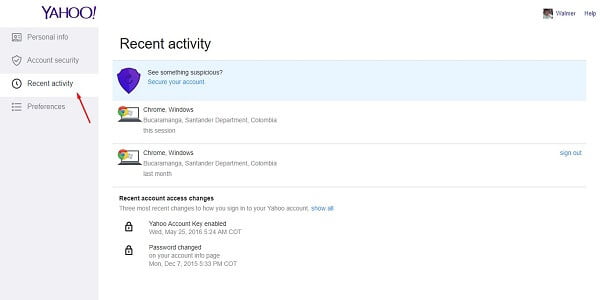
In the same order of ideas, these data are extremely valuable especially if it is suspected that someone is having access to the account with not authorization what so ever. In fact, the registration activity even allow to control sessions that have remained opened on other devices, something especially useful if a session stayed opened on a PC or device that is not trusted in first place.
In order to conclude, not only that information can be supervised but also the applications that are linked to Yahoo account, such as social networks and email apps on smartphones. In last place, it is also registered if there have had password changes and the context from where it happened, for example, if access was not allowed and password has been modified through recovery function, or if the change has been carried out through the procedure on the previous title.

Related posts